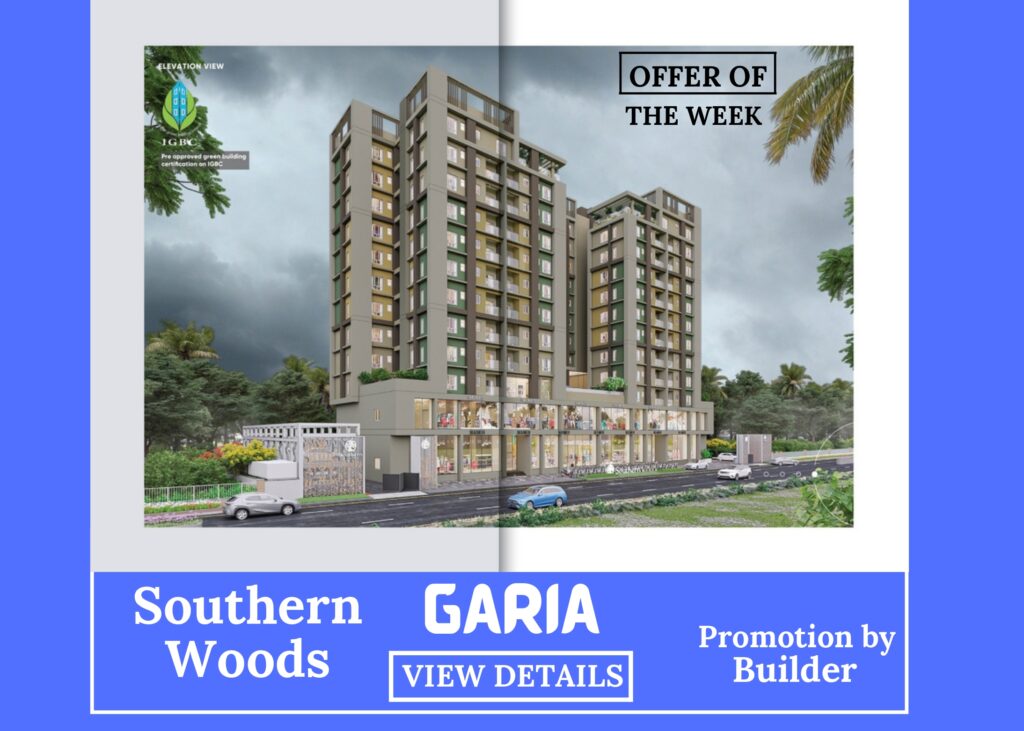
Metro Management has now proceeded to construct exclusive Southwinds with several builders as per their recent projects. These flats are about to be finished with construction works and are in ready-to-move condition. The process will be completed by the first half of 2024.
Metro Management is another name for trust and reliability in the sectors of real estate properties. We are working with several builders to give you the best properties of your choice. Go through the following content to know more about why you should choose us as your property advisor.S
Other Facility
- 24-hour water supply
- Adequate car parking space for residents and visitors
- CCTV for enhanced security
- ISI marked reputed steel
- Anti Skid ceramic tiles for the washroom
- Aluminum/UPVC casement windows
- Vitrified tiles
- Flush door
- Copper wiring
- Branded elevators
- RCC frame structure
- Sanitary fittings
- Black Granite kitchen platform
Area:
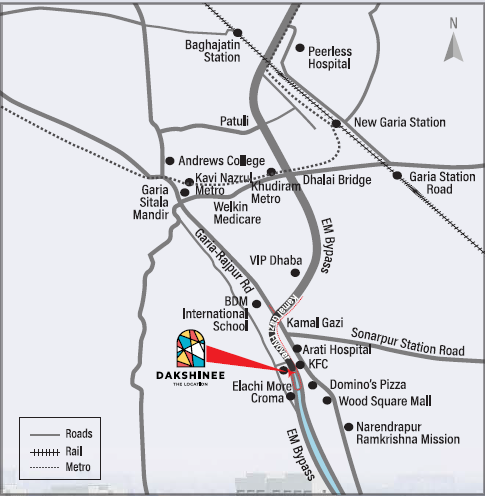
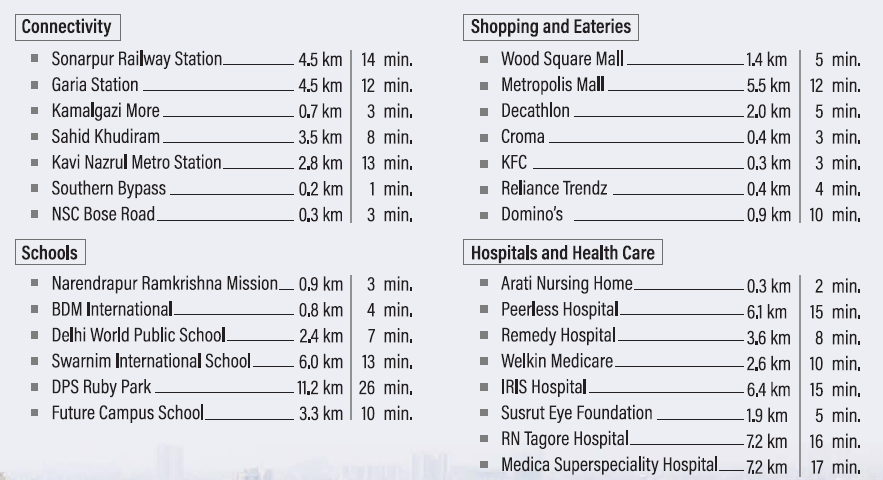
Garia is a developing part of South Kolkata on the banks of Adi Ganga. It falls under Kolkata Municipal Corporation and Rajpur Sonarpur Municipality. Being a blooming part of this area is constructed with all types of facilities including public transport and residential areas.
New Garia, Garia Park, Chak Garia, Baghajatin, Baishnabghata-Patuli, Ajoy Nagar, Techno City, Model Town, Ganguly Bagan, are prime residential areas in Garia. Many rising apartment complexes, shopping malls, educational institutions, government organizations are building in this competitively new settlement. Most importantly this part of the city is connected by railway station, bus terminals, and metro station.
All facilities are found in these newly organized settlements. So the demands of properties in Garia are high. Residential properties starts here from 20 lakh which increases as 0er
Our properties are situated to give you the utmost facility of communication in Garia. All modes of transportation and public vehicles like the train station, metro station, and bus facilities are just within a walking distance from your residence.
We are Working with Several Renowned Builders:
We are working with several renowned builders like:
Devaloke Group is selling 1107 to 1460 sq ft carpet area at the base selling price of ₹50 lakhs to ₹62 lakhs.
Multicon Group sells carpet areas ranging in size from 1194 to 1327 square feet for between 50 and 55 lakhs.
Primarc Srijan Group is selling 1136 to 1376 sq ft carpet area at the base selling price of ₹55 lakhs to ₹66 lakhs.
Atri Group sells carpet areas ranging in size from 950 to 1000 square feet for between 44 and 52 lakhs.
Ideal Group is selling 1175 to 1285 sq ft carpet area at the base selling price of ₹52 lakhs to ₹67 lakhs.
Daffodil Group is selling carpet areas ranging from 1165 to 1210 square feet for a starting price of 43 lakhs to 48 lakhs.
Rajwada Group is selling 1060 to 1424 sq ft carpet area at the base selling price of ₹52 lakhs to ₹67 lakhs.
Sureka Group is selling carpet areas ranging from 820 to 995 square feet for a starting price of 5o lakhs to 62 lakhs.